Ex-employees still had access: An offboarding checklist

At a company I worked at, we discovered that former employees still had active accounts. Not one or two people who left last month. Dozens. Some had quit over a year earlier. Their credentials worked just fine on email, file sharing, CRM, internal tools - the lot.
Nobody revoked their access when they left. There was no process for it. HR ticked their offboarding boxes - final paycheck, exit interview, collect the laptop. But the digital side? No checklist. No owner. No one even thought about it until an IT audit surfaced the mess.
The question you can't answer
Here's what made this genuinely unsettling. When we checked, some of those accounts had been logged into on a fairly regular basis. Former employees - people who no longer worked for us - were actively accessing our systems. Our customer list, pricing data, internal financials, product roadmap - all of it accessible to people we had no control over. Some of whom left on less than amicable terms.
Did a former sales rep sell our customer list to a competitor? It's entirely possible. Did a disgruntled developer poke around in systems they shouldn't have? We could see logins, but not what they did once inside.
That's worse than a confirmed breach. With a breach, you know what happened and you can respond. Here, we knew the door was open and people were walking through it - we just couldn't tell what they took.
Why this keeps happening
Offboarding is one of those things every company assumes is handled. The manager thinks HR does it. HR thinks IT does it. IT never got the memo the person left.
In SMEs, this is particularly rampant. You're big enough that not everyone knows everyone, but small enough that there's no automated identity management system. People fall through the cracks constantly. A contractor finishes their engagement and nobody tells IT. An intern's last day comes and goes. A senior hire quits during a busy quarter and the cleanup never happens.
The common thread is always the same: no single person owns the offboarding process end to end, and there's no system making the invisible visible.
What proper offboarding actually looks like
It's not complicated. When someone leaves, three things need to happen the same day.
- First, deactivate every account. Email, Slack, cloud storage, CRM, code repositories, admin panels - everything. Not next week. That day. Make a list of every system and check them off one by one.
- Second, revoke physical access. Collect keycards, fobs, keys. Change codes if they had them. This is the one thing most companies actually remember, ironically.
- Third, transfer ownership of their files, projects, and contacts. Don't just lock the account and let critical information vanish into a digital void.
The hard part isn't doing these three things. It's making sure they happen every single time, for every single departure. That requires a process with a clear owner, a checklist that can't be skipped, and visibility when something is overdue.
Reminders aren't enough
This is the same lesson I learned from the office lease debacle. Sending someone an email saying "don't forget to deactivate accounts" is not a process. It's a hope.
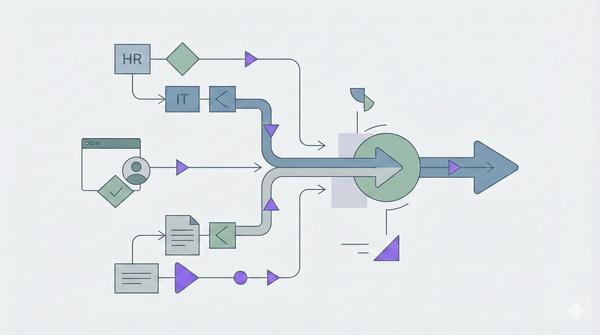
You need a system that assigns the task, tracks completion, escalates when it's late, and gives leadership a dashboard showing what's done and what isn't. Not a system that fires one notification and moves on.
This is one of the core problems I'm building Process Oak to solve. We launch in 2026 - join the waitlist at processoak.com.